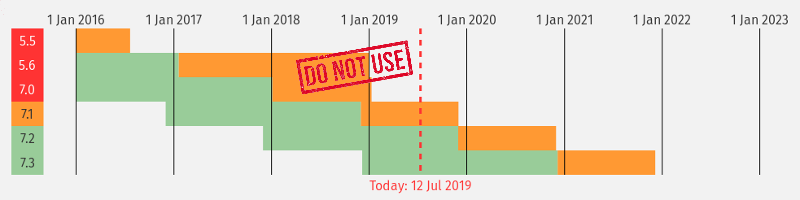
As of December 2018 PHP 5 and 7.0 became End of Life. It is now July 2019 and up to 74% of PHP powered sites in the top 1 million are running software that is End of Life. This means there is no support and more importantly if new vulnerabilities are discovered, there will be no security fixes released.
Upgrades do take work and major updates can take even more work. People are busy and the reluctance for patching when things are just working is understandable. However, when things go End of Life, there are no more valid reasons to not upgrade. In fact, with the latest releases of PHP there are a number of benefits to upgrading including a significant increase in site speed.
PHP End of Life Stats
Methodology
During July we performed a semi regular analysis of WordPress usage in the top 1 million sites. The methodology for this process is to download the default page from the top 1 million sites and performing analysis on the HTTP headers and HTML source of the resulting pages.
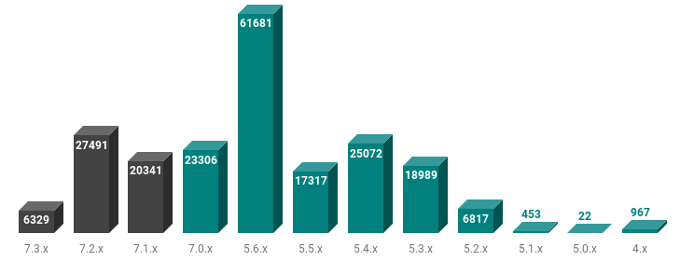
The following data is based on sites that reveal the PHP version in the HTTP headers.
The number of sites running unsupported PHP is staggering. Especially considering these are among the highest traffic sites in the world. If a serious security vulnerability were to be discovered in PHP core or a module, these sites would have no way to patch and get protected.
Just show me the Stats!
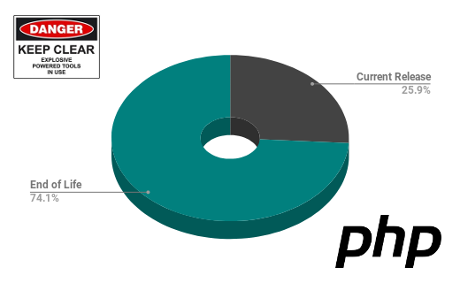
We found 208806 sites leaking the PHP version of these 154645 are running a version that does not include PHP/7.1 or PHP/7.2 or PHP/7.3.
This is where we get the figure of 74% of sites running PHP that is currently End of Life (unsupported).
PHP versions and WordPress
WordPress will require a minimum PHP version of 7 by the end of the year. This matters because WordPress runs close to 30% of all websites accounting for a large percentage of PHP powered sites.
According to statistics from wordpress.org 37.1% are running End of Life PHP. There is however no detail as to how the version was determined.
Another popular content management system Drupal recommends a minimum PHP version of 7.1.
Important Caveat
Newer versions of PHP do hide the version by default through the expose_php Off directive in the php.ini file, so in the overall PHP statistics we would expect the percentage to be better than the 74% shown in the data we have.
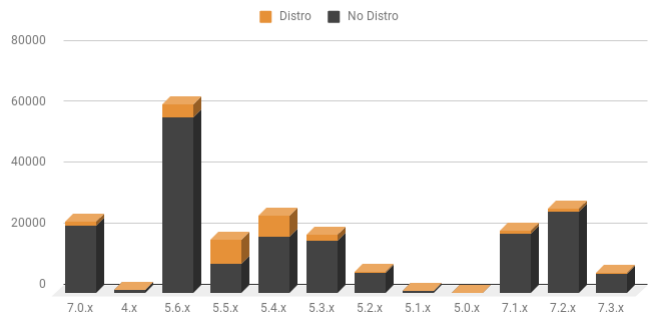
Distributions such as Red Hat, Ubuntu, and Debian can provide security patching to packaged PHP even if the version is no longer supported through the official PHP project. An example of this is ongoing support provided as part of the Ubuntu LTS (long term support) releases. Distribution packaged PHP reveals the distribution in the X-Powered-By and Server: headers.
Examples: X-Powered-By: PHP/5.6.30-0+deb8u1 Server: Apache/2.4.6 (Red Hat Enterprise Linux) OpenSSL/1.0.1e-fips PHP/5.5.38 X-Powered-By: PHP/5.5.9-1ubuntu4.29 Server: Apache/2.4.6 (CentOS) OpenSSL/1.0.1e-fips PHP/5.6.40
Checking for these Linux distributions shows 25532 sites are using the distributions packaging (this does not verify that these are all supported but some would be). In the chart below you can see the versions with a number using a distribution package for the PHP software.
PHP Vulnerabilities
At the time of the article there are currently 599 PHP vulnerabilties with CVE's. The chart below shows number of PHP vulnerabilities discovered with a CVE score of 6 or higher by month.
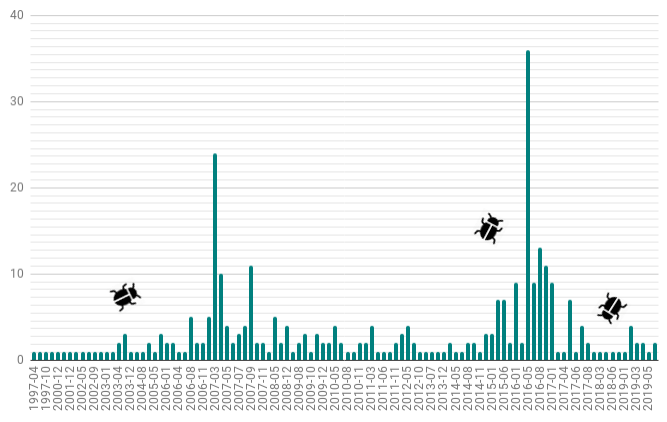
As can be seen over the years there has been a steady stream of vulnerabilities discovered. Of course this is the case in any popular and complex piece of software, whether it is commercial or open source software. This is here as simply another reminder that it is time to upgrade your PHP to a current release.
Comparing Microsoft IIS End of Life
For a quick comparison against a very different software environment we examined Microsoft IIS server versions. The IIS web server version aligns closely with the Windows Server releases as can be seen in the table below.
The statistics are based on Microsoft IIS versions found in our survey of the Alexa top 1 million sites.
Total Microsoft-IIS Powered Sites: 67787 (6.8% of top 1M)
Microsoft IIS 7.5 or earlier versions accounts for 30.3% of sites.
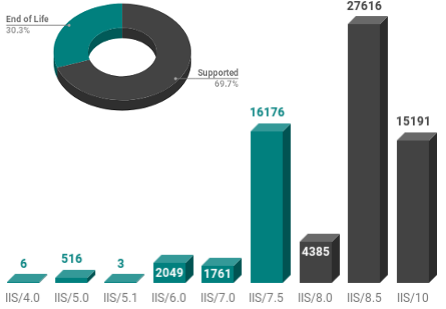
| IIS Version | # of sites | Windows Version |
|---|---|---|
| IIS/4.0 | 6 | Windows NT4.0 with options pack (End of Life) |
| IIS/5.0 | 516 | Windows 2000 (End of Life) |
| IIS/5.1 | 3 | Windows XP Professional (End of Life) |
| IIS/6.0 | 2049 | Windows Server 2003 and XP (End of Life) |
| IIS/7.0 | 1761 | Windows Server 2008 (End of Life) |
| IIS/7.5 | 16176 | Windows Server 2008 R2 (End of Life) * |
| IIS/8.0 | 4385 | Windows Server 2012 |
| IIS/8.5 | 27616 | Windows Server 2012 R2 |
| IIS/10.0 | 15191 | Windows Server 2016 & 2019 |
* IIS/7.5 is covered by Extended Security Updates until January 14 2020. Extended Security Updates (ESU) are available for the Datacenter, Standard, and Embedded editions of this product, for up to an additional three years past the end of support.
Conclusion
Even if we take into account the caveats and accept that the number would be lower than 74% across all PHP based sites, it is clear that a significant number of sites do need to upgrade. Site administrators need to get to work and fix this issue now. A new vulnerability could appear any day, and if you are not running a support version then that will be a bad day.
Knowing your vulnerability exposure and what services are listening on your network is the first step in keeping your organisation secure. Our service simplifies that first step with hosted online vulnerability scanners. Try it out today. Immediate access is available with a full refund available within 7 days.
Next Level Your Technical Network Intelligence
-
13 Vulnerability Scanners -
17 Free DNS & Network Tools -
4+ Billion Records of DNS / IP data