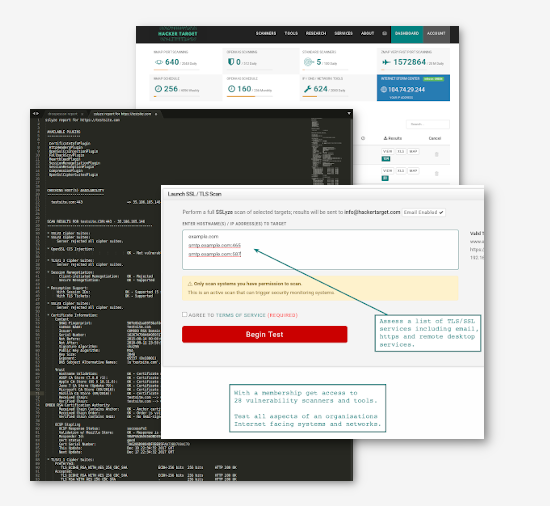
Check SSL/TLS services for vulnerabilities and weak ciphers with this online SSL Scan. Makes use of the excellent sslyze and OpenSSL to gather the certificate details and measure security of the SSL/TLS implementation.
Identifying known vulnerabilities and cryptographic weakness with certain SSL/TLS implementations such as SSLv2 and weak ciphers is an important part of the vulnerability assessment process. This hosted service enables a server to be easily tested for known security problems with the configuration, whether you are testing one server or a network.
Free SSL / TLS Scan to check the ciphers in use, certificate validity and configuration errors.
Test any SSL/TLS based services (https / smtps / pop3s / ftps) to gain immediate insight into the hosts security posture. With a membership test services in bulk with SSLyze for all known vulnerabilities.
- Certificate Information
- Valid & Trusted Cert Check
- Identify SSL/TLS protocols in use
- Enumerate Ciphers
Membership Benefits
Tap into the potential for advanced exploitation or vulnerability assessment of web servers and websites with exclusive access.
Cryptographic weakness
Discover known cryptographic weakness in TLS/SSL services
Certificate details
Analyze SSL/TLS and Retrieve Certificate Info.
SSL / TLS vulnerabilities
Identify known SSL / TLS vulnerabilities.
OSINT
Access to 27 Vulnerability Scanners and OSINT Tools
Configuration errors
Test for SSL/TLS configuration errors
Open Source Tools
Trusted Open Source Tools
About the Online SSL Scan and Certificate Check
What this tool testsSSL/TLS encrypts communication between clients and servers, most visibly HTTPS in browsers, but also email (SMTP/POP), FTP, VPNs and any TCP protocol. Weaknesses in these protocols have been discovered and exploited for decades, making configuration and version support critical.
This scanner uses sslyze to test any SSL/TLS-enabled host and port, identifying both protocol-level design flaws (like POODLE and DROWN) and software-specific implementation bugs (like Heartbleed).
- Weak or deprecated protocols : SSLv2, SSLv3, TLS 1.0/1.1 (all should be disabled)
- Certificate validity : expiry, trust chain, hostname match
- Known vulnerabilities : Heartbleed, BEAST, CRIME, BREACH, DROWN, FREAK, POODLE and more
- Cipher suite strength : flagging weak or export-grade ciphers
PCI DSS requires SSLv2, SSLv3 and TLS 1.0 to be disabled. TLS 1.2 and TLS 1.3 are the current standards.
"The primary benefit of transport layer security is the protection of web application data from unauthorized disclosure and modification when it is transmitted between clients (web browsers) and the web application server, and between the web application server and back end and other non-browser based enterprise components."
- OWASP Transport Layer Protection Cheat Sheet
Other TLS/SSL testing tools include:
- Nmap : ssl-enum-cipers and ssl-cert NSE scripts
- TestSSL.sh : free tool, bash-based, no dependencies, runs anywhere.
- OpenVAS (GVM) full vulnerability scan suite including SSL/TLS checks.
Common SSL/TLS Vulnerabilities and Attacks
This timeline shows notable SSL/TLS vulnerabilities, from early padding oracle attacks to modern protocol and implementation flaws.While newer standards like TLS 1.3 have addressed many historical issues, misconfigurations and legacy support continue to expose systems to risk.
SSL/TLS attack timeline
1998 – 2026 · Click any attack pill to expand details
Legend
Bleichenbacher Million Message Attack
Padding oracle attack on PKCS#1 v1.5, the RSA padding standard in SSL/TLS. Daniel Bleichenbacher demonstrated recovery of encrypted messages from SSLv3 using between 300k–2M ciphertexts, impractical in the wild due to the sheer number of connections required. That limitation is exactly what DROWN later solved. Planted the seed for DROWN and ROBOT.
Vaudenay CBC Padding Oracle (EUROCRYPT 2002)
Serge Vaudenay exposed a fundamental flaw in CBC construction. He demonstrated that SSL/TLS's MAC-then-Pad-then-Encrypt CBC construction leaks padding validity via error responses, enabling decryption one byte at a time. It served as the theoretical foundation for major attacks such POODLE, Lucky13, Zombie POODLE, and GOLDENDOODLE.
Attacking RSA-based Sessions in SSL/TLS (CHES 2003)
Extended Bleichenbacher's attack with a second-level oracle checking TLS version fields rather than padding. Made RSA session key recovery more practical in specific TLS implementations.
HTTPS Downgrade via sslstrip · Black Hat USA 2009 · Moxie Marlinspike
A MITM attacker silently downgrades HTTPS to HTTP by hijacking the initial plaintext request before TLS is ever negotiated. The victim never knows. Directly motivated HSTS (HTTP Strict Transport Security).
TLS Renegotiation Attack (CVE-2009-3555)
No cryptographic binding existed between an initial TLS handshake and any renegotiated handshake. An attacker could inject arbitrary plaintext at the start of a TLS session, enabling credential theft on servers accepting client-initiated renegotiation.
Browser Exploit Against SSL/TLS · Juliano Rizzo & Thai Duong
A MITM attack using JavaScript or applet injection into the same origin exploits predictable IVs in CBC mode under TLS 1.0 and SSLv3, recovering session cookies and authentication details. RC4 was initially recommended as a mitigation, but RC4's own weaknesses proved a greater risk than BEAST itself, ultimately leading the banning of RC4 entirely.
Compression Ratio Info-leak Made Easy · Juliano Rizzo & Thai Duong
Demonstrated by the researchers behind BEAST, CRIME targets HTTP request headers by exploiting TLS/SPDY compression (DEFLATE/GZIP/LZ77). By measuring ciphertext length to guess characters, an attacker can leak session cookies byte-by-byte, effectively ending TLS-level compression influencing HTTP/2's adoption of the attack-resistant HPACK standard.
Lucky Thirteen · Al Fardan & Paterson
A timing side-channel in TLS's CBC-mode MAC processing. Even implementations that had patched Vaudenay's 2002 padding oracle remained vulnerable. Lucky Thirteen reopened the same class of attack by exploiting the 13-byte TLS record header in MAC computation timing.
Browser Reconnaissance and Exfiltration via Adaptive Compression of Hypertext · Gluck, Harris & Prado
Built on the logic of CRIME, BREACH targets HTTP response body compression (GZIP). By observing ciphertext length changes as reflected secrets are guessed, an attacker can exfiltrate CSRF tokens or other response body secrets in under 30 seconds. Because the flaw is application-level, it works against any TLS version including TLS 1.3. HEIST (2016) later proved no MITM network position is required.
Timing Info-leak Made Easy · Tal Be'ery & Amichai Shulman (Imperva)
A timing-based padding oracle attack on CBC mode in TLS, TIME recovers HTTP cookies by measuring server response times rather than requiring network eavesdropping. Any malicious site can launch it against its own visitors simply by controlling the plaintext. Closely related to the Lucky Thirteen research (Al Fardan & Paterson, 2013).
Padding Oracle On Downgraded Legacy Encryption · Bodo Möller, Thai Duong & Krzysztof Kotowicz (Google)
Exploits a padding flaw in SSLv3 CBC mode combined with protocol downgrade. A MITM attacker forces a downgrade to SSLv3 then recovers cookies and passwords. SSLv3 persisted for legacy reasons. POODLE ended that, formalised by RFC 7568 in 2015.
OpenSSL Heartbeat Extension Vulnerability
Widely considered one of the biggest Internet vulnerabilities in recent history. A flaw in OpenSSL's heartbeat extension, designed to keep TLS sessions alive without renegotiation, allowed attackers to read up to 64KB of server memory per request, with no limit on repeat attacks and no trace left. The attacker sends 1KB claiming it is 64KB; the server replied with 64KB including 63KB of raw memory, potentially exposing private keys, session tokens, and passwords. No authentication required.
Unlike the protocol design flaws on this timeline, Heartbleed was a single coding error in OpenSSL. The fallout forced a global industry audit of critical open-source security dependencies and directly led to the creation of LibreSSL and BoringSSL.
Factoring Attack on RSA-EXPORT Keys
In the 1990s, US export regulations capped RSA keys at 512 bits. Researchers discovered these weak export keys were still accepted by many web servers (Apache, IIS, nginx and others), any server allowing export cipher suites was potentially vulnerable. A MITM attacker forces a downgrade to 512-bit RSA, factors the key, and decrypts the session.
Logjam — Weak Diffie-Hellman Attack
Targets 512-bit DH export cipher suites. MITM tricks the server into using weak DH, then decrypts the session. Even modern browsers can be tricked into accepting export grades.
RC4 Stream Cipher Prohibition (RFC 7465)
RC4 was once recommended as a BEAST mitigation, but accumulated weaknesses made it worse than the attacks it was meant to prevent. RFC 7465 prohibited RC4 Cipher Suites in all TLS versions.
Decrypting RSA with Obsolete and Weakened eNcryption
A modernised Bleichenbacher attack targeting RSA key reuse between modern TLS and obsolete SSLv2 services. By using a co-hosted SSLv2 endpoint as a padding oracle, researchers decrypted modern TLS traffic in hours rather than months. DROWN proved that modern connections are only as secure as the weakest protocol sharing the same private key.
HTTP Encrypted Information can be Stolen through TCP-windows · Mathy Vanhoef & Tom Van Goethem
Uses TCP window sizes to measure the exact length of encrypted responses via malicious JavaScript, no MITM network position required. By turning the browser into a measuring tool, HEIST enables BREACH and CRIME-style attacks against both HTTP/1 and HTTP/2. It does not break the TLS encryption directly instead, it leaks data via the compression side-channel.
Security Losses from Obsolete and Truncated Transcript Hashes · Karthikeyan Bhargavan & Gaëtan Leurent
Exploits weak RSA-MD5 signatures still accepted by some TLS 1.2 stacks. A MITM attacker executes a transcript collision attack by downgrading to these obsolete hash functions.
Birthday Attack on 64-bit Block Ciphers · Karthikeyan Bhargavan & Gaëtan Leurent
A birthday attack against legacy 64-bit block ciphers (3DES, Blowfish). A MITM attacker uses malicious JavaScript to generate ~32GB of traffic within a realistic browsing session, enough to exploit CBC block collisions and recover session cookies. 32GB sounds large but is a surprisingly achievable threshold for modern web sessions, contributing to the deprecation of 64-bit ciphers in favour of AES.
Return Of Bleichenbacher's Oracle Threat · Disclosed Dec 2017 · Hanno Böck, Juraj Somorovsky & Craig Young
Proved the 1998 Bleichenbacher RSA padding oracle was still exploitable in major TLS implementations nearly two decades later, affecting 27 of the top 100 web domains including Facebook and PayPal. Only affects TLS cipher modes using RSA key exchange, not ECDHE.
RFC 8446 · August 2018
TLS 1.3 is a major protocol rewrite that removes several vulnerability classes by eliminating the underlying mechanisms, rather than patching individual flaws.
- No RSA key exchange: mandatory forward secrecy via Diffie-Hellman kills the Bleichenbacher, ROBOT, and DROWN lineage.
- No CBC mode: AEAD ciphers (AES-GCM, ChaCha20-Poly1305) replace CBC, eliminating the POODLE and Lucky Thirteen padding oracle family.
- No TLS compression: formally banned, closing the door on CRIME at the protocol level. BREACH, which targets HTTP-level compression rather than TLS compression, remains an application-layer concern requiring separate mitigation.
- Encrypted handshake: server certificates are now encrypted in transit, significantly limiting metadata visible to network observers.
Resurrected CBC Padding Oracle
A slight tweak to POODLE's padding oracle still worked against a major Citrix load balancer in 2019 — years after POODLE was supposedly patched. Presented at Black Hat Asia 2019.
GOLDENDOODLE — Faster CBC Padding Oracle
A faster, more powerful cousin to Zombie POODLE. Exploits CBC padding oracles in TLS 1.0–1.2 to decrypt session cookies much faster than classic POODLE. Also Black Hat Asia 2019.
Raccoon Attack — TLS 1.2 DH Timing Oracle
Timing side-channel in TLS 1.2's Diffie-Hellman key exchange. Server-side timing differences leak information about the premaster secret, enabling session decryption under specific conditions. Difficult to exploit in practice.
Application Layer Protocol Confusion — Cracks in TLS Authentication
TLS doesn't bind a connection to its intended application-layer protocol. An MITM attacker redirects HTTPS traffic to a wildcard-cert-sharing FTP or email server, stealing cookies or triggering XSS. 1.4M servers found vulnerable.
Sample SSLyze Results
The following output shows the results from the sslyze tool against the hackertarget.com domain.
As you can see a number of different tests are performed against the service to check for common SSL vulnerabilities.
CHECKING CONNECTIVITY TO SERVER(S)
----------------------------------
www.hackertarget.com:443 => 172.67.72.147
SCAN RESULTS FOR WWW.HACKERTARGET.COM:443 - 172.67.72.147
---------------------------------------------------------
* Certificates Information:
Hostname sent for SNI: www.hackertarget.com
Number of cert chains detected: 2 (ECPublicKey, RSAPublicKey)
Certificate Chain #1 (ECPublicKey)
SHA1 Fingerprint: 172c9f4de7ce08af80ab60da387bfcaec176da94
Common Name: hackertarget.com
Issuer: WE1
Serial Number: 209660902455163680101493000012837199109
Not Before: 2026-03-31
Not After: 2026-06-29
Public Key Algorithm: ECPublicKey
Signature Algorithm: sha256
Key Size: 256
Curve: secp256r1
SubjAltName - DNS Names: ['hackertarget.com', '*.hackertarget.com']
Certificate Chain #1 - Trust
Android CA Store (15.0.0_r9): OK - Certificate is trusted
Apple CA Store (iOS 18, iPadOS 18, macOS 15, tvOS 18, visionOS 2 and watchOS 11):OK - Certificate is trusted
Java CA Store (jdk-13.0.2): OK - Certificate is trusted
Mozilla CA Store (2024-11-24): OK - Certificate is trusted
Windows CA Store (2023-12-11): OK - Certificate is trusted
Symantec 2018 Deprecation: OK - Not a Symantec-issued certificate
Received Chain: hackertarget.com --> WE1 --> GTS Root R4
Verified Chain: hackertarget.com --> WE1 --> GTS Root R4
Received Chain Contains Anchor: OK - Anchor certificate not sent
Received Chain Order: OK - Order is valid
Verified Chain contains SHA1: OK - No SHA1-signed certificate in the verified certificate chain
Certificate Chain #1 - Extensions
OCSP Must-Staple: NOT SUPPORTED - Extension not found
Certificate Transparency: WARNING - Only 2 SCTs included but Google recommends 3 or more
Certificate Chain #1 - OCSP Stapling
OCSP Response Status: SUCCESSFUL
Validation w/ Mozilla Store: OK - Response is trusted
Responder Key Hash: b'\x90w\x925g\xc4\xff\xa8\xcc\xa9\xe6{\xd9\x80y{\xcc\x93\xf98'
Cert Status: GOOD
Cert Serial Number: 209660902455163680101493000012837199109
This Update: 2026-04-20
Next Update: 2026-04-27
Certificate Chain #2 (RSAPublicKey)
SHA1 Fingerprint: b638230c50ae0ae1a30fe61645a74b0782cc13e9
Common Name: hackertarget.com
Issuer: WR1
Serial Number: 336240350818015599941775461382858464611
Not Before: 2026-03-31
Not After: 2026-06-29
Public Key Algorithm: RSAPublicKey
Signature Algorithm: sha256
Key Size: 2048
Exponent: 65537
SubjAltName - DNS Names: ['hackertarget.com', '*.hackertarget.com']
Certificate Chain #2 - Trust
Android CA Store (15.0.0_r9): OK - Certificate is trusted
Apple CA Store (iOS 18, iPadOS 18, macOS 15, tvOS 18, visionOS 2 and watchOS 11):OK - Certificate is trusted
Java CA Store (jdk-13.0.2): OK - Certificate is trusted
Mozilla CA Store (2024-11-24): OK - Certificate is trusted
Windows CA Store (2023-12-11): OK - Certificate is trusted
Symantec 2018 Deprecation: OK - Not a Symantec-issued certificate
Received Chain: hackertarget.com --> WR1 --> GTS Root R1
Verified Chain: hackertarget.com --> WR1 --> GTS Root R1
Received Chain Contains Anchor: OK - Anchor certificate not sent
Received Chain Order: OK - Order is valid
Verified Chain contains SHA1: OK - No SHA1-signed certificate in the verified certificate chain
Certificate Chain #2 - Extensions
OCSP Must-Staple: NOT SUPPORTED - Extension not found
Certificate Transparency: WARNING - Only 2 SCTs included but Google recommends 3 or more
Certificate Chain #2 - OCSP Stapling
OCSP Response Status: SUCCESSFUL
Validation w/ Mozilla Store: OK - Response is trusted
Responder Key Hash: b'fiI\xd4\xde*\x9c\x91\x03\xcf\x89\x0e$\xb8\x0e0\x03n\x88.'
Cert Status: GOOD
Cert Serial Number: 336240350818015599941775461382858464611
This Update: 2026-04-20
Next Update: 2026-04-27
* SSL 2.0 Cipher Suites:
Attempted to connect using 7 cipher suites; the server rejected all cipher suites.
* SSL 3.0 Cipher Suites:
Attempted to connect using 80 cipher suites; the server rejected all cipher suites.
* TLS 1.0 Cipher Suites:
Attempted to connect using 80 cipher suites.
The server accepted the following 5 cipher suites:
TLS_RSA_WITH_AES_256_CBC_SHA 256
TLS_RSA_WITH_AES_128_CBC_SHA 128
TLS_RSA_WITH_3DES_EDE_CBC_SHA 168
TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA 256 ECDH: prime256v1 (256 bits)
TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA 128 ECDH: prime256v1 (256 bits)
The group of cipher suites supported by the server has the following properties:
Forward Secrecy OK - Supported
Legacy RC4 Algorithm OK - Not Supported
* TLS 1.1 Cipher Suites:
Attempted to connect using 80 cipher suites.
The server accepted the following 4 cipher suites:
TLS_RSA_WITH_AES_256_CBC_SHA 256
TLS_RSA_WITH_AES_128_CBC_SHA 128
TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA 256 ECDH: prime256v1 (256 bits)
TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA 128 ECDH: prime256v1 (256 bits)
The group of cipher suites supported by the server has the following properties:
Forward Secrecy OK - Supported
Legacy RC4 Algorithm OK - Not Supported
* TLS 1.2 Cipher Suites:
Attempted to connect using 156 cipher suites.
The server accepted the following 20 cipher suites:
TLS_RSA_WITH_AES_256_GCM_SHA384 256
TLS_RSA_WITH_AES_256_CBC_SHA256 256
TLS_RSA_WITH_AES_256_CBC_SHA 256
TLS_RSA_WITH_AES_128_GCM_SHA256 128
TLS_RSA_WITH_AES_128_CBC_SHA256 128
TLS_RSA_WITH_AES_128_CBC_SHA 128
TLS_ECDHE_RSA_WITH_CHACHA20_POLY1305_SHA256 256 ECDH: X25519 (253 bits)
TLS_ECDHE_RSA_WITH_AES_256_GCM_SHA384 256 ECDH: prime256v1 (256 bits)
TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA384 256 ECDH: prime256v1 (256 bits)
TLS_ECDHE_RSA_WITH_AES_256_CBC_SHA 256 ECDH: prime256v1 (256 bits)
TLS_ECDHE_RSA_WITH_AES_128_GCM_SHA256 128 ECDH: prime256v1 (256 bits)
TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA256 128 ECDH: prime256v1 (256 bits)
TLS_ECDHE_RSA_WITH_AES_128_CBC_SHA 128 ECDH: prime256v1 (256 bits)
TLS_ECDHE_ECDSA_WITH_CHACHA20_POLY1305_SHA256 256 ECDH: X25519 (253 bits)
TLS_ECDHE_ECDSA_WITH_AES_256_GCM_SHA384 256 ECDH: prime256v1 (256 bits)
TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA384 256 ECDH: prime256v1 (256 bits)
TLS_ECDHE_ECDSA_WITH_AES_256_CBC_SHA 256 ECDH: prime256v1 (256 bits)
TLS_ECDHE_ECDSA_WITH_AES_128_GCM_SHA256 128 ECDH: prime256v1 (256 bits)
TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA256 128 ECDH: prime256v1 (256 bits)
TLS_ECDHE_ECDSA_WITH_AES_128_CBC_SHA 128 ECDH: prime256v1 (256 bits)
The group of cipher suites supported by the server has the following properties:
Forward Secrecy OK - Supported
Legacy RC4 Algorithm OK - Not Supported
* TLS 1.3 Cipher Suites:
Attempted to connect using 5 cipher suites.
The server accepted the following 3 cipher suites:
TLS_CHACHA20_POLY1305_SHA256 256 ECDH: X25519 (253 bits)
TLS_AES_256_GCM_SHA384 256 ECDH: X25519 (253 bits)
TLS_AES_128_GCM_SHA256 128 ECDH: X25519 (253 bits)
* OpenSSL Heartbleed:
OK - Not vulnerable to Heartbleed
SCANS COMPLETED IN 3.203003 S
-----------------------------
COMPLIANCE AGAINST MOZILLA TLS CONFIGURATION
--------------------------------------------
Disabled; use --mozilla_config={old, intermediate, modern}.
Vulnerability Scans & Network Intelligence
Map your attack surface, enumerate hosts, and identify open vulnerabilities across your perimeter.
Use CasesEnumerate & Discover
Know the Network
Resolve DNS records, geolocate IPs, trace network paths, and uncover ASN ownership for any target.
IP & DNS Tools28 Scanners & Network Tools
Unlock the full toolkit; automated scans, DNS enumeration, port scanning, and more.
View Membership