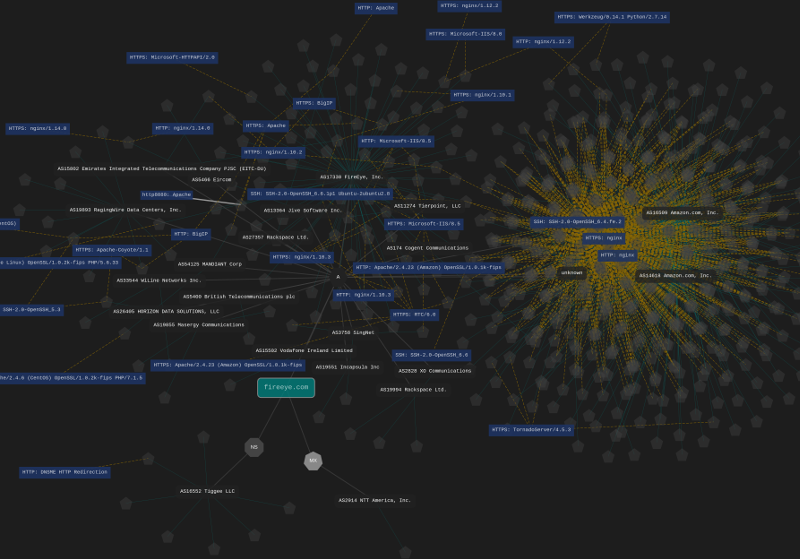
Typical clients include both Enterprise and Small / Medium Enterprises (SME), anyone with more than a handful of Internet facing services will get immediate value from this type of assessment. Starting from a single domain or organization name we review open source intelligence (OSINT) sources and Internet Wide Scan data to develop an attack surface. That is end points where a targeted attacker would be probing to get access to your systems and data.
The target of this assessment is network resources, systems and endpoints. There is no targeting of organisations members or employees for social engineering purposes.
An attacker targeting your organisation has access to this intelligence. Do you?
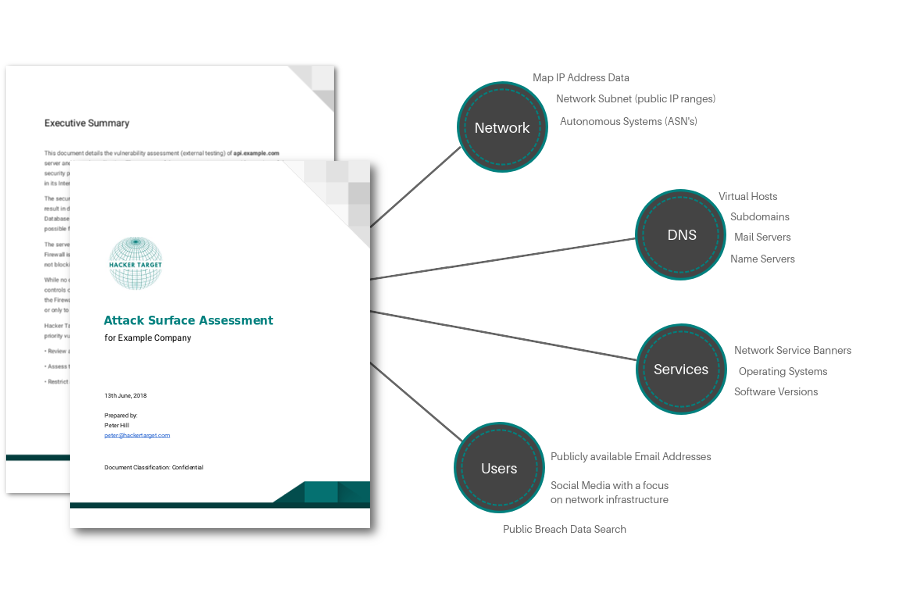
The report will be delivered as a PDF and a Spreadsheet and contain:
- Discovered Host names
- Discovered IP addresses and Network Blocks
- Discovered open services (from Internet wide Scan Data not active port scans)
- Email addresses found in breach data sets, including details on breach and information compromised
- Metadata from documents, code leaks, S3 Buckets and other information leaks relevant to the organisation
- Related Security & Network Information sourced from open source (OSINT)
Another third party assessment we offer is a focused External Vulnerability Assessment. This involves active vulnerability scanning and validation of the detected vulnerabilities.