DNS & IP Tools provide tactical intelligence to the Security Operation Center (SOC) and Penetration Testers. Use these tools to map the attack surface of a target, identify security weaknesses, and streamline incident response. Quickly collect data on IP Addresses, Networks, Web applications and DNS records.
These information gathering tools serve as tactical reconnaissance tools. Quickly gather relevant information and pivot into deeper enumeration using port scanners, web page analysis and other more aggressive tools.
Automation & Integration: All tools are accessible via the web forms below or through our easy to use API, third party integrations (Splunk, Maltego etc), and the official Chrome extension.
IP and Network Tools
All tools available via web form and API. No sign-up required for free access.
Click a tool name for detailed notes and example results.
Network tests
Trace path hop-by-hop with latency.
Network path analysis and latency troubleshooting.
api.hackertarget.com/mtr/?q={target}
Round-trip time and packet loss.
Connectivity testing and availability checks.
api.hackertarget.com/ping/?q={target}
DNS
Resolve Standard Records for a Domain (A, MX, NS, TXT).
Initial reconnaissance and domain analysis.
api.hackertarget.com/dnslookup/?q={target}
Reverse lookup an IP or IP range.
Infrastructure correlation and threat actor profiling.
api.hackertarget.com/reversedns/?q={target}
Discover subdomains and A records.
Subdomain enumeration and attack surface mapping.
api.hackertarget.com/hostsearch/?q={target}
Test for DNS AXFR leaks.
Identify DNS misconfigurations and data exposure.
api.hackertarget.com/zonetransfer/?q={target}
Registrant and ASN details.
Ownership identification and domain history.
api.hackertarget.com/whois/?q={target}
IP Address
Country, City and ISP data.
Geographic attribution and infrastructure mapping.
api.hackertarget.com/geoip/?q={target}
Find hostnames on the same IP.
Find domains sharing the same hosting infrastructure.
api.hackertarget.com/reverseiplookup/?q={target}
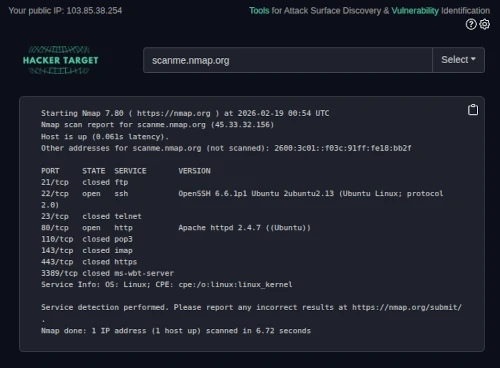
Scan common TCP ports.
Attack surface enumeration and firewall analysis.
api.hackertarget.com/nmap/?q={target}
Scan common UDP ports.
UDP service discovery and exposure analysis.
api.hackertarget.com/nmap/?q={target}&udp=1
Calculate network ranges and CIDR.
Network range calculation and CIDR analysis.
api.hackertarget.com/subnetcalc/?q={target}
ASN, Owner, and IP range lookup.
Autonomous system identification and BGP analysis.
api.hackertarget.com/aslookup/?q={target}
Service version fingerprinting.
Service fingerprinting and version detection.
api.hackertarget.com/bannerlookup/?q={target}
Web Tools
Server and security header audit.
Web application fingerprinting and security header audit.
api.hackertarget.com/httpheaders/?q={target}
Extract all links from a URL.
Link discovery and web crawl preparation.
api.hackertarget.com/pagelinks/?q={target}
Many of these tools are passive, meaning no packets are sent directly to the target IP ranges. For tools that do generate traffic, scanning from our infrastructure provides an abstraction layer between your own IP range and the target. This is particularly useful for investigations or Red Team operations where non-attribution is a priority.
To ensure service availability and minimize abuse, the following limits apply to the Free tier:
- Web Access: Ad-hoc queries via the individual tool forms.
- API Access: Rate-limited automation for rapid reconnaissance.
- Quotas: Free users are limited a maximum of 50 API calls per day (depending on the tool).
IP Tools API Documentation
The HackerTarget API streamlines access to network intelligence for security evaluation. All tools listed in the table above are accessible using your client of choice such as curl, a web browser or a scripting language (php, python).
Quick Start (No Auth)
Free access requires no sign-up or API key. Simply append the target IP or hostname to the q= parameter.
- Output Formats: Plain Text (Default) or JSON (selected endpoints).
- Clients: Compatible with
curl, python, php, or any standard HTTP client.
Member Authentication
Members get full access to the API endpoints. Find your API key in the user dashboard. Access with the API key must use HTTPS.
Authentication can be handled via two methods:
- Query Parameter:
Append the key directly to the URL string using the &apikey= parameter:
https://api.hackertarget.com/dnslookup/?q=example.com&apikey=YOUR_KEY
- HTTP Header:
Pass the key in the request header using X-API-Key:
X-API-Key: YOUR_KEY
Example requests
Use these standard curl patterns to integrate the tools into your workflow:
curl "https://api.hackertarget.com/dnslookup/?q=hackertarget.com&apikey=plmoknijbuhvygvtrgedsfghhhhkjhkhfsk"
curl -H "X-API-Key: zzzzzzaaaaaaaa" "https://api.hackertarget.com/whois/?q=hackertarget.com"
Example: Examining Headers
test@thematrix:~$ curl -i https://api.hackertarget.com/geoip/?q=1.1.1.1
HTTP/2 200
server: nginx
date: Thu, 19 Feb 2026 01:17:26 GMT
content-type: text/plain; charset=utf-8
content-length: 78
x-api-quota: 51
x-api-count: 8
x-api-boost: 100 000
access-control-allow-origin:*
IP Address: 1.1.1.1
Country: Australia
Latitude: -33.494
Longitude: 143.2104
Automate reconnaissance with Domain Profiler
Run all of these tools against a target domain in a single pass. Domain Profiler chains DNS, Whois, reverse IP, port scanning and more into one automated report.
Useful when you need a full picture of an organisation's Internet-facing infrastructure quickly.
View Domain Profiler
Service Limits & Quota Monitoring
The current users API quota and usage can both be monitored by examining the HTTP Headers of the response from the API endpoint. The curl -i command will display the HTTP Headers as part of the output. The x-api-quota reports on the current users API quota and the x-api-count shows the current API usage count for the day.
To ensure reliability and prevent abuse, the following constraints apply to all API requests.
Rate Limits & Headers
- Free daily cap
- 50 calls per day
- Rate limit
- 2 req/s — breach returns
HTTP 429
- Caching
- Some endpoints — see ToS
- x-api-quota
- Total daily allowance
- x-api-count
- Calls used today
- x-api-boost
- Purchased credits remaining
Boost API Credits
Available now for all Members. Credits activate automatically once your daily quota is exhausted. Membership allowance always applies first.
Pro
BEST VALUE
1,000,000 credits
Contact Sales to Order
hackertarget.com/ip-tools/
Chrome Extension for Fast Access to IP Tools
Instant intelligence, without leaving your tab.
DNS, Whois, IP Geolocation, Port Scan and more. One click away directly in Chrome.
Download from Chrome Store
Frequently Asked Questions
Common questions about the tools, API limits and membership.
Yes. All 18 tools are free via the web forms with no sign-up required. Free users get API access limited to 50 calls per day from a single IP. Membership removes this limit, unlocks higher quotas, unlimited results (free capped at 500 lines), and 28 additional vulnerability scanners.
Free users: 50 calls/day, max 2 req/s. Exceeding returns HTTP 429. Members get higher quotas. Additional credits: 100,000 for $250 USD or 1,000,000 for $1,400 USD — activating automatically once the daily quota is exhausted.
Free access needs no authentication. Members use their API key from the
user dashboard via query parameter (
&apikey=YOUR_KEY) or HTTP header (
X-API-Key: YOUR_KEY). Must use HTTPS.
Every API response includes usage headers. Use curl -i to inspect. x-api-quota shows your daily allowance, x-api-count shows calls made today, x-api-boost shows remaining purchased credits.
Many are passive. DNS Lookup, Whois, IP Geolocation, Reverse IP and AS Lookup send no packets to the target. Active tools including Traceroute, Ping, TCP/UDP Port Scan and Banner Grabbing originate from HackerTarget infrastructure, providing an abstraction layer useful for non-attribution operations.
Plain text by default, compatible with curl, Python, PHP, or any HTTP client. Selected endpoints also support JSON. All follow the pattern: https://api.hackertarget.com/{tool}/?q={target}
Click any tool name in the table above. Each individual tool page includes example output.
The
Domain Profiler automates reconnaissance in a single pass incl DNS, Whois, reverse IP, port scanning and more, with
visual network diagrams showing domain, subdomain and IP relationships. Individual tools require manual pivoting. Available to members.
Yes. HackerTarget provides third party integrations (Splunk, Maltego etc) for pivot-based workflows and an official
Chrome extension for in-browser access. The API works with any HTTP client including
curl, Python
requests and PHP.
-
2.75 Billion Host A records
-
2.1 Billion Network Service Banners
-
2 Million Vulnerability Scans performed per year